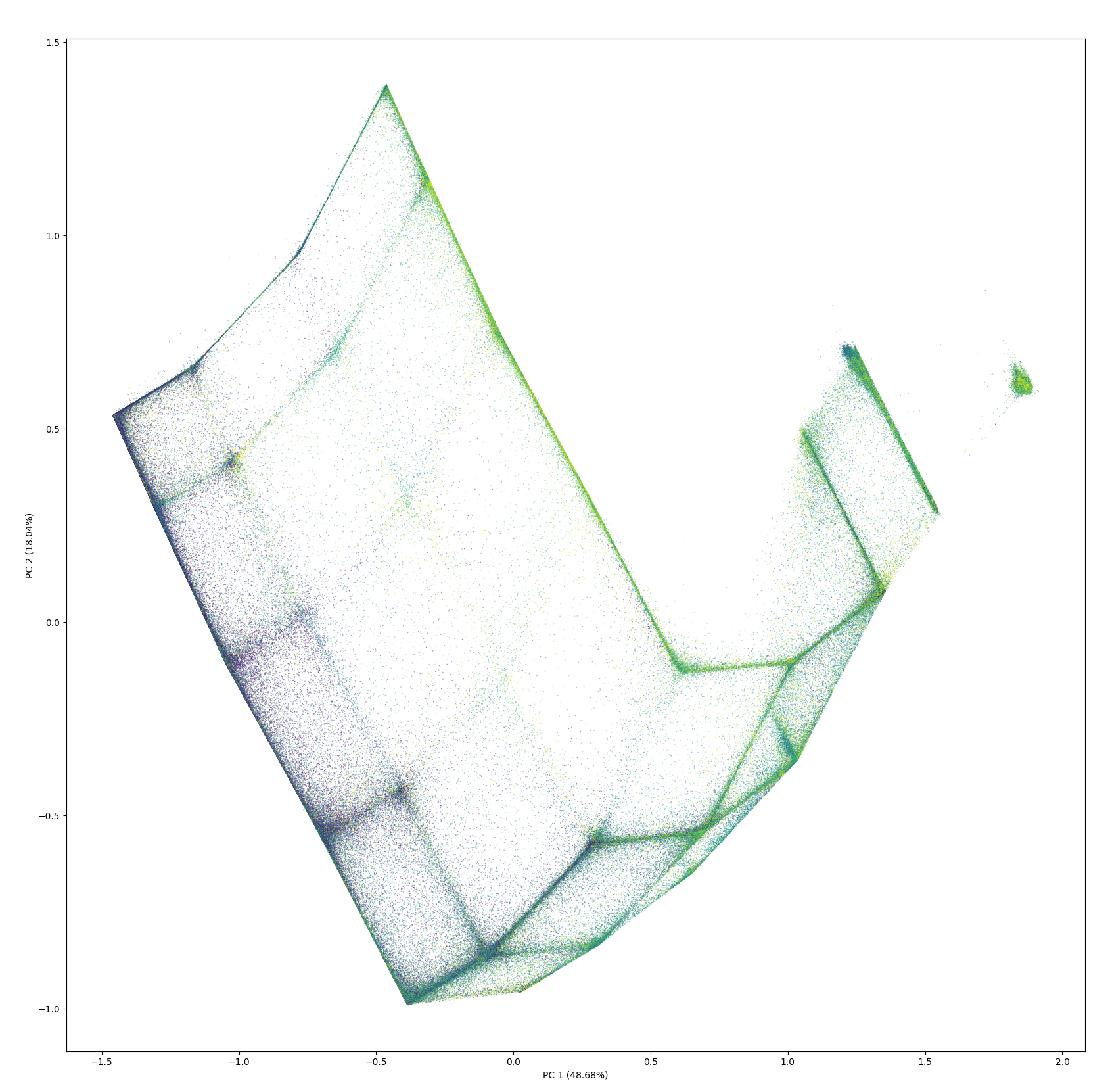
I'm a Principal Research Scientist at the Alan Turing Institute, where I lead work on technical AI safety-in particular cyber risk-and technical AI governance. My focus is how general-purpose AI changes offensive cyber capability, and how to evaluate and mitigate those risks in ways that hold up technically and in policy.
My recent work on proportional AI evaluations was published in Science, and I contributed to a benchmark of expert-level questions assessing AI capabilities published in Nature. I lead the AI Cyber Risk Benchmark and was the lead author of the cyber offence section of the International AI Safety Report with Yoshua Bengio (2024-25 and 2025-26).
I work at the research-policy interface, contributing to systemic risk evaluation practice at the EU AI Office, informing UK Parliament's resilience strategy for critical infrastructure, and supporting the Turing's early-access safety testing of frontier models.
I work at the research-policy interface, contributing to systemic risk evaluation practice at the EU AI Office, informing UK Parliament's resilience strategy for critical infrastructure, and supporting the Turing's early-access safety testing of frontier models. I'm Area Editor (AI Security) for the Journal of Cybersecurity.
If you're working on AI risk, cyber security, or evaluation of emerging capabilities-especially in high-stakes settings like critical infrastructure-feel free to reach out; I follow an ikigai approach and prioritise work with high expected impact.